Analyzing Rig Exploit Kit
First
When I began writing this article, I didn't know that Talos is writing detailed articles about RigEK. I read it after I finished writing this article, but it was a very nice and detailed analysis report. If you want to do a detailed analysis on RigEK, I recommend you refer to that article.http://blog.talosintelligence.com/2016/11/rig-exploit-kit-campaign-happy-puzzling.html
This article is a memo to keep information that is somewhat concisely summarized about RigEK for me in the future who will write a college graduation thesis after a few months ;)
Step 0
There is a pcap that I captured by myself, but pcap that Brad organized is more beautiful than that, so I will use it. I appreciate Brad every day. Thank you for writing about the Drive-by Download attack and Exploit Kit.Download pcap from Malware-traffic-analysis.
http://www.malware-traffic-analysis.net/2017/04/16/index.html
Step 1
Kindly enough, zip contains html of Landing Page, but let's investigate in order this time.First, I look at the end of html obtained when accessing the Compromised site, then a script is injected that tells it is EITest at first sight.
With this script tag "side[.]chobaniandyr[.]com" is read in iframe.
Step 2
Let's see the Landing page of the loaded RigEK. You will see obfuscated code that is very verbose and difficult for humans to read.As you can see from reading the code, this code consists of three JavaScript elements. I will call them Part 1, Part 2, Part 3. In the previous version of RigEK it was not divided into three parts, only Part 3 existed. Please refer to the RSA analysis article for details.
https://community.rsa.com/community/products/netwitness/blog/2017/02/01/rig-ek-chronology-of-an-exploit-kit
It is divided into three below.
Step 3
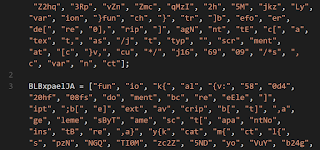
The obfuscation logic of Part 1~3 is common, it is very simple. Here I show the procedure to cancel obfuscation only for Part 3, which has the smallest code amount. In the same way Part 1 and Part 2 can also cancel obfuscation.First of all, a string containing a lot of unfamiliar symbols appears, but it is split with a character string that is not familiar. By doing the following, it will become visually easy to understand.
As you can see from here, by combining the first array and the second array, a new JavaScript is generated. In other words, JavaScript retrieves the first array in reverse order and concatenates them to the second element, respectively. Such processing will be done in subsequent processing.
When I read the code, it try to dynamically generate JavaScript code and execute it with eval. If you get the character string passed to eval with Part 1~3, it will be as follows.
I could decipher the obfuscation of the first step. Let's decipher the following obfuscation.
Step 4
Obfuscation at the second stage is easy. You can see at a glance by looking at the code. It is only obfuscated by Base64. The result of decoding the base64 encoded character string is as follows.Step 5
I will analyze each part. In the following, Part 1 is VBScript, Part 2 is JavaScript (VML), Part 3 is JavaScript (Flash), but the order seems random. In each part, they strike the vulnerability of each application and let it execute arbitrary code. As a result, malware is dropped and infected.Part1
There is a great article below about this.http://marcoramilli.blogspot.jp/2017/03/a-quick-revenge-analysis.html
Part2
There is a great article below about this.http://binaryhax0r.blogspot.jp/2016/09/rig-exploit-kit-shellcode-spwans.html
Part3
I am ignorant about swf, so I omit it.Finally
In this way, RigEK sends malware to users with a bit of obfuscation and multiple exploit codes. Perhaps after a few days or weeks these contents will change with RigEK updates. If I could observe it, I would write another article again.Have a good analysis day😉
 nao_sec
nao_sec